TXT DKIM Signing Feature
By creating and applying an aligned DKIM signature for each of your sending domains, you can significantly improve the trust of your messages in the eyes of the mailbox providers.
The DKIM signature will only be applied when the DKIM signature is an exact match to the From address.
The process of creating a DKIM signature starts by creating a private and public DKIM key pair.
Configuring "Bring your own TXT record" DKIM
We have simplified this process through our DKIM Key Generator. During the process, the generator will ask you to choose a 'selector value'. This value should only be alphanumeric characters, and we recommend fewer than 10 total characters. It serves as a name that you will use to refer to the DKIM keys you are creating.
Configuring "Generate your own TXT record" DKIM
Even further simplified is the "Generate your own TXT record" option. When this option is selected, SocketLabs will generate and populate the key pair. The private key will be automatically added to your SocketLabs account. The public key will be provided to be added to DNS.
Once the public key is successfully added to DNS and the DKIM signature is saved to the SocketLabs server, the public key will no longer be accessible within the portal.
The boxes for Split Record and Escape Records below the key selector field are dependent on your hosting provider. If you are unsure and it does not populate at first with both boxes unchecked; you can try each different combination.
Once you have your private/public key pair, the next step is to create a DNS entry on your domain to publish the public key.
Example
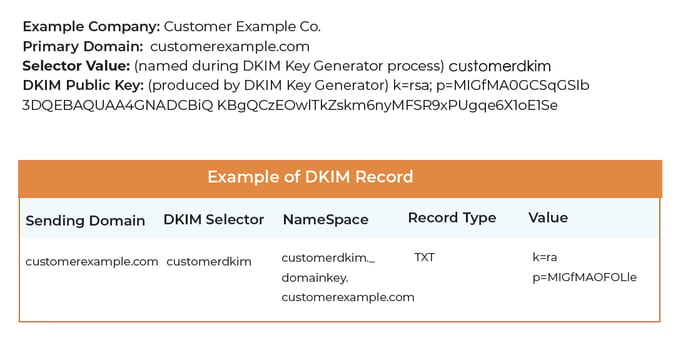 After creating the necessary DNS entries, add the following information into the appropriate fields under "Bring your own TXT record" in your SocketLabs account. (If you selected "Generate your own TXT record", this information was auto-populated.)
After creating the necessary DNS entries, add the following information into the appropriate fields under "Bring your own TXT record" in your SocketLabs account. (If you selected "Generate your own TXT record", this information was auto-populated.)
- DKIM Domain/Sending Domain
- DKIM Selector
- DKIM Private Key (produced during DKIM Key Generator process)
The SocketLabs On-Demand Control Panel will not allow you to save the settings until it can verify the public key based on the domain and selector provided.
Related Information
For more information about DKIM authentication technology please see our other article: DomainKeys Identified Mail (DKIM) Authentication
For more information about SPF authentication please see our related article: Sender Policy Framework (SPF)
